When privacy faces the security on the battlefield:
the story of how privacy is being sacrificed with security related justifications in digital realm
Introduction
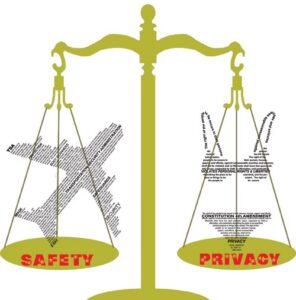
Security and privacy, two terms that usually we hear interchangeably in academic literatures or discussions of the digital world. While the former refers to the body of technologies, processes or practices designed to protect assets, programs, and data from attack, damage or unauthorized access, the latter is focused on the use and governance of personal data, things like putting policies in place to ensure consumers’ right to their personal information against being collected, shared, or used in the way the owner of the data don’t want. Mostly, these two terms have been introduced as complementary to one another to offer a reliable system. However, there are some cases they confront each other. It ranges from surveillance systems aiming to guarantee national security to the security of novel technologies. This blog post discuss how hunger for further security in different applications (in specific biometric) invade citizens’ privacy. I should note that this blog post might have been written with a critical point of view, but it is not definitely a practice to discourage study new science or labor negatives too hard. The driving force behind this text is to look for an answer more than keeping the balance between security and privacy.
Why to raise this topic?
In current era, individuals’ personal data are constantly being accumulated by different means of monitoring such as surveillance cameras, tracking applications, health gadgets, etc. This issue has raised different privacy concerns because people think their privacy rights are at the stake. When it comes to national security, there are merely no right and wrong answers, since the balance between security and privacy is incredibly delicate. On one hand, these monitoring activities potentially provide extra security, on the other hand, they are not justifiable for violating human rights and cause insecurity among people. However, the accumulation of personal data and hence privacy concerns are not limited only to the domains like national security or let’s call it cases with collaborative benefits. For instance, in light of better security for biometric recognition, privacy is being sacrificed in some state-of-the-arts. The example that I selected to delve into in this text and describe how it subjects individuals to privacy leakage is behavioral biometrics.
Behavioral biometric
If it’s not the most important, but definitely authentication is one of the most critical security measures in any systems for granting access to their user. It is defined as the process of recognizing an individual’s identity, a mechanism to associate the incoming request with a set of identifying credentials to an authorized user within the system. In biometric systems, multiple ways of authentication called verification has been studied during past decades. The main group of these methods is focused on capturing and processing physical traits of subjects (e.g., fingerprint, retina, face, iris, hand geometry, etc.) while the other group is considering behavioral characteristics (e.g., gait (the way someone is walking), signature, keystroke). In recent years, behavioral biometrics has been evolved by introducing new features to be captured. For instance, in mobile behavioral biometric, background sensor data like accelerometer, gravity sensor, gyroscope, touchscreen data, etc. are being collected from user mobile device. One of the well-known applications of behavioral biometric is continuous authentication, in which the data of these sensors are constantly being captured and processed to make the owner stay authenticated. This is a method to provide authentication, justifying that it offers more convenience while addressing physiological biometric limits found in conventional approaches. But at what cost?
I would like to pause here and ask you how much are you willing to sacrifice your privacy to be more comfortable with authentication? Even in terms of security benefits compared to conventional methods, how much security continuous authentication provides us and how much privacy it deprives of us? In other words, does its security advantages outweigh the privacy risks? Technologies like continuous authentication with behavioral biometrics, continuously monitor and study individual’s state of mind to conclude whether they are the same person. Under best conditions, are we ready to let new technologies like this peep into our personal life and study all psychological aspects of our characteristic just to bring us more security at most with our bank account? What if these sensitive personal data leak or being processed by giant tech companies without our permission or even get accessed by authorities with the justifications like national security? Falling at the disposal of undemocratic or corrupted governments, this technology would be a mean of modern slavery. These are some few examples of many questions about privacy concerns that spring to mind, but important to be answered before proceeding with this technology.
What is the solution then?
So far, you might think I’m obviously not a fan of behavioral biometrics, but this is a mere example of many current research lines that have been explored and applied in real-world scenarios without answering to privacy concerns properly. On the other hand, I don’t really mean to only give the cliché answer of let’s keep the balance between privacy and security. The best solution still is to use the privacy protection mechanisms, providing that they can address aforementioned questions. From my point of view, novel technologies with privacy concerns shall not be employed in real-world cases until most of these respective concerns are being dealt with. In particular, one should assure users with preserving their privacy using a defense in depth strategy. In other words, various privacy protection methods like obfuscation, full anonymity, using of pseudonyms, differential privacy should be adopted jointly before introducing new technologies into people’s daily life. Apart from technical solutions, we need to raise awareness about the risks of using novel technologies. It is quite obvious that there is no panacea either regarding security or privacy that can assure 100% protection against all threats. Therefore, in parallel with scientific attempts, people need to be informed not only with respect to privacy hazards of the technologies they are using in their daily life but also about their privacy rights specially in digital domains.
This blogpost was written by Mahdi Ghafoorian.